至于翻译我等等会送上!!请各位稍后!!Monday, January 2, 2012Details on Corona Now that Corona was released by the iPhone Dev Team and the Chro
nic Dev Team, I can give details a
bout how it works.1. the user land exploitApple has fixed all previous known ways of executing unsigned binaries in iOS 5.0. Corona does it another way.By the past, the trick security researchers used was to include the untethering payload as a data page (as opposed to a code page) in the Mach-O binary. The advantage of a data page was that the Macho-O loader didn
't check its authenticity. ROP is used so that code execution happens without writing executable code but rather by utilizing existing signed code in the dyld cache. To have the ROP started by the Mach-O loader, they relied on different technics found by @comex, either :- the interposition exploit- the initializer exploitHere is a detailed explanation of incomplete code sign tricks used before 5.0 : http://theiphonewiki.com/wiki/index.php?title=Incomplete_Codesign_ExploitIn iOS 5.0, data pages need also to be signed by Apple for the loader to authenticate the binary. @i0n1c seems to be able to pass through these verifications though (https://twitter.com/#!/i0n1c/status/145132665325105152). We may see this in the 5.1 jailbreak.Thus, for Corona, I searched for a way to start unsigned code at boot without using the Mach-O loader. That
's why I looked for vulnerabilities in existing Apple binaries that I could call using standard launchd plist mechanisms.Using a fuzzer, I found after some hours of work that there
's a format string vulnerability in the racoon co
nfiguration parsing code! racoon is the IPsec IKE daemon (http://ipsec-tools.sourceforge.net/). It comes by default with iOS and is started when you setup an IPsec connection.Now you got it, Corona is an anagram of racoon :-) .By the way, the exploitation of the format string vulnerability is different than what was done in 2001, check it out if you
're interested !For the jailbreak to be applied at boot, racoon is started by a launchd plist file, executing the command : racoon -f racoon-exploit.confracoon-exploit.conf is a large co
nfiguration file exploiting the format string bug to get the unsigned code started.The format string bug is utilized to copy the ROP bootstrap payload to the memory and to execute it by overwriting a saved LR in the racoon stack by a stack pivot gadget.The ROP bootstrap payload copies the ROP exploit payload from the payload file which is distributed with Corona then stack pivot to it. The idea is to escape from format strings as fast as possible, because they are CPU time consuming.The ROP exploit payload triggers the kernel exploit.2. the kernel exploitThe kernel exploit relies on an HFS heap overflow bug I found earlier. I don
't know exactly what happens in the kernel code, I never figured it out exactly, I found it by fuzzing the HFS btree parser.I just realized that it is a heap overflow in the zone allocator, so I started to try to mount clean, overflowed and payload images in a Heap Feng Shui way :-) And hey, that worked :p Thanks to @i0n1c for his papers on this subject. This helped me a lot. I may have given up without them.The kernel heap overflow exploit copies 0
x200 bytes from the vnimage.payload file to the kernel sysent replacing a syscall to a write anywher
e gadget. Some syscalls (first 0
xA0 bytes and the last 0x6 bytes) are trashed in the operation because I needed to respect the HFS protocol.Thus, I restore them as fast as possible to get a stable exploit, then the write anywher
e is used to copy the kernel exploit and jump to it.The kernel exploit just patches the kernel security features, as usual. Nothing interesting there.Happy New Year 2012 to you all,??thanks a lot for the donations.~pod2g=700) window.open('http://images.tgbus.com/attachments/photo/Day_120103/19780_fe551325561623b25389339e7e56a.png');" o
nload="if(this.offsetWidth>'700')this.width='700';if(this.offsetHeight>'700')this.height='700';" >=700) window.open('http://images.tgbus.com/attachments/photo/Day_120103/19780_d222132556163501442002b46a420.png');" o
nload="if(this.offsetWidth>'700')this.width='700';if(this.offsetHeight>'700')this.height='700';" >=700) window.open('http://images.tgbus.com/attachments/photo/Day_120103/19780_d222132556163501442002b46a420.png');" o
nload="if(this.offsetWidth>'700')this.width='700';if(this.offsetHeight>'700')this.height='700';" >=700) window.open('http://images.tgbus.com/attachments/photo/Day_120103/19780_fe551325561623b25389339e7e56a.png');" o
nload="if(this.offsetWidth>'700')this.width='700';if(this.offsetHeight>'700')this.height='700';" >1.苹果已修复所有先前已知的方式的 iOS 5.0 中执行无符号的二进制文件. Corona运用了另外一种方式.安全研究人员使用的是包括拴系的有效载荷数据页(而不是一个代码页)在mach-o二进制。利用一个数据页,macho-o装载机不检查其真实性。早产儿视网膜病变是用来使代码执行的发生是没有写作可执行代码而是通过利用现有的签名代码在dyld缓存. 他们依靠不同的工程从而发现了它!发现者是@comex,,同时comex也发现了一种简便通用的快速干涉检查算法和预置(初始状态), 初始化 模式2.这是一个详细的要点,解释了内置代码的意思(在5.0之前).网页参考:http://theiphonewiki.com/wiki/index.php?title=Incomplete_Codesign_Exploit3.在ios5,数据也需要签署苹果为装载机验证二进制。“i0n1c似乎能够通过这些验证.4.因此,Corona我寻找一种方式开始签名代码在开机不使用mach-o装载机。这就是为什么我找漏洞现有苹果的二进制文件可以使用标准的launchd编辑机制。使用模糊测试工具,我发现经过几个小时的工作,有一个格式化字符串漏洞在浣熊配置解析代码!浣熊是艾克的守护进程(网址://ipsec-toolsforge。。网)。这是默认行为开始时,你设置一个安全连接。5.现在你有它,Corona是一字谜浣熊:(很好的比喻哟!!)越狱的被应用在启动,Corona是开始由一个launchd编辑文件,执行命令:Corona-女racoon-exploit.conf(racoon-exploit.conf是一个大的配置文件利用格式化字符串漏洞得到签名代码开始。)6.格式化字符串漏洞是用来复制罗普引导有效载荷的记忆和执行它所覆盖,保存或在堆栈的Corona.7.机械钻速举载荷副本罗普利用有效载荷的有效载荷文件上分布有电晕堆栈支点它。这个想法是逃离格式字符串尽快,因为他们是中央处理器时间。()这个我也不会翻译只好上网自己翻译了!!效果不太好!!))见谅内核开发内核开发依靠HFS溢出错误发现前。我不知道到底会发生什么在内核代码,我从来没有理解了它,我发现它的模糊HFS分析器。我才意识到,这是一个堆溢出的区域分配器,于是我开始尝试装入干净,溢出和有效载荷的图像在一堆风水的方式:-)嘿,工作:磷感谢@i0n1c他的关于这个问题的论文。这帮助了我很多。我也许已经放弃了他们。仁堆溢出的副本返回码字节从vnimage.payload文件内核系统调用一个写三个更换任何小工具。一些调用(第一0
xa0字节,最后0x6字节)的垃圾在运作,因为我需要尊重网络协议。因此,我使他们尽快得到一个稳定漏洞(内核),然后写入任何用于复制内核和跳转到它。内核利用补丁的内核的安全功能,如往常一样。有什么有趣的。2012新年快乐你的一切,感谢很多的捐款。~pod2g
网友回复================================
坐等翻译…沙花…
网友回复================================
Hen 不错, 很详细, 谢谢!原来是USER LAND级别的漏洞.IPSec工具中racoon 模块的一个漏洞.
网友回复================================
引用 引用第2楼qinray于2012-01-03 11:44发表的:Hen 不错, 很详细, 谢谢!原来是USER LAND级别的漏洞.IPSec工具中racoon 模块的一个漏洞.......=700) window.open('http://images.tgbus.com/images/back.gif');" onload="if(this.offsetWidth>'700')this.width='700';if(this.offsetHeight>'700')this.height='700';" >
是啊!因为ios5改变了验证方式,所以就会之前4.0运用的那个漏洞软件就会失效了!不过当他们开发立刻一个新的search漏洞的工具后,一切都是浮云了!

 乐趣不输电子游戏台北国际电玩展桌游区热度盛况空前
乐趣不输电子游戏台北国际电玩展桌游区热度盛况空前 暴雪国服停服国游瓜分空白市场监管边际改善游戏股预期估值修复
暴雪国服停服国游瓜分空白市场监管边际改善游戏股预期估值修复 吃鸡2个月花30000会怎样光子亲发见面礼有5种福利
吃鸡2个月花30000会怎样光子亲发见面礼有5种福利 梦幻西游普通装备暗藏玄机一个月刷60亿的角色你见过么
梦幻西游普通装备暗藏玄机一个月刷60亿的角色你见过么 策划终于对韩信下手了其实还真不冤枉原来韩信出场率已经登顶
策划终于对韩信下手了其实还真不冤枉原来韩信出场率已经登顶 骚白又要挑战吉尼斯记录了回归KS后十号开播还有百万现金放送
骚白又要挑战吉尼斯记录了回归KS后十号开播还有百万现金放送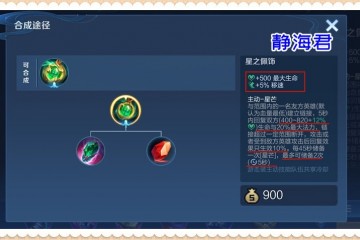 王者荣耀打脸太快星泉效果远超想象孙膑已然成为一线辅助
王者荣耀打脸太快星泉效果远超想象孙膑已然成为一线辅助 散兵是原神第一个觉醒者生日阵仗太大国内外齐庆生
散兵是原神第一个觉醒者生日阵仗太大国内外齐庆生